If you’re already using Azure Active Directory (AD) for multi-factor authentication, integrating your VPN is the next smart move. More and more of our clients are shifting from on-prem authentication to Azure AD VPN integration with Cisco AnyConnect. For many good reasons.
You get:
-
Granular control over who can log in remotely
-
Seamless sign-in with your users’ existing Azure AD credentials
-
Centralized management (no more collecting logs from on-prem servers)
-
Better visibility and simplified admin tasks
It’s a win for security, user experience, and IT time.
What You’ll Need to Get Started
Before you dive in, make sure you have the following:
-
An Azure AD subscription (free version available)
-
Cisco AnyConnect SSO enabled (available via the Azure Gallery)
-
Cisco ASA firmware version 9.7(1) or higher
Note: If you’re running a load-balanced VPN, you’ll need ASA version 9.16 or newer.
Step 1: Add Cisco AnyConnect to Azure AD
Once you’re ready to go, the first step is to add The Cisco AnyConnect app to Azure AD form the Application Gallery.
-
- Sign in to the Azure with your work or school account.
- On the left navigation pane, go to Azure Active Directory > Enterprise Applications > All Applications.
- Click New Application.
- Search for Cisco AnyConnect in the gallery.
- Select it and wait while it installs to your tenant.
Step 2: Configure SAML-Based Single Sign-On
Now we have to configure and enable the AnyConnect Integration.
-
- In your new Cisco AnyConnect app, go to Single Sign-On.
- Choose SAML as your sign-on method.
- Click the pencil icon to edit Basic SAML Configuration.
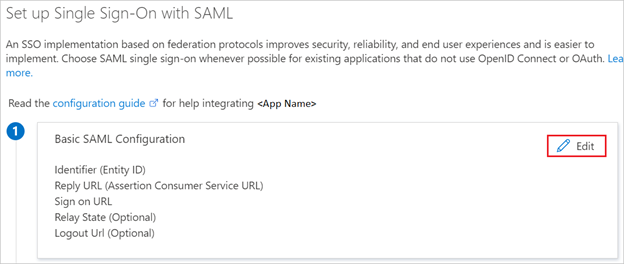
4. Enter your settings. Identifier (Entity ID) and Reply URL follow a specific format based on your tunnel group name. If you have multiple tunnel groups, you’ll need to create a separate app entry for each.
In the Identifier text box, type a URL using the following pattern:
In the Reply URL text box, type a URL using the following pattern:
⚠️ Make sure your tunnel group name doesn’t contain dots or slashes, and note it’s case-sensitive.
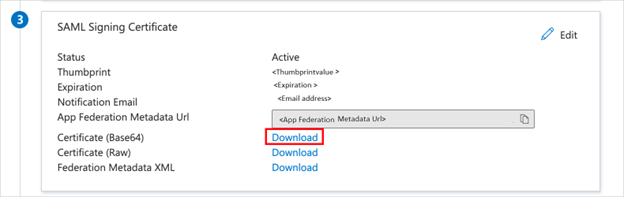
5. Under SAML Signing Certificate, download the Base64 certificate
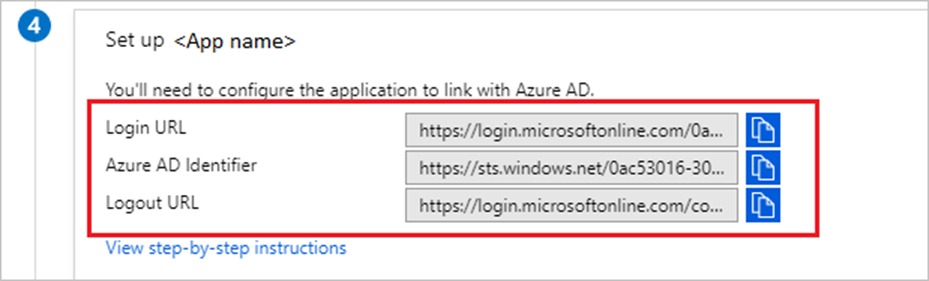
6. Copy the appropriate SAML URLs shown for your setup
Step 3: Assign Users or Groups to the VPN
Now we need to add either a test user or the group we want to enable for the VPN to the Cisco AnyConnect application.
-
- In the Azure portal, select Enterprise Applications > All applications > Cisco AnyConnect.
- In the app’s overview page, find the Manage section > Users and groups > Add User.
- In the Users and Groups dialog, select your test user or VPN group from the Users list.
- If you are expecting a role to be assigned to the users, you can select it from Select a Role. If no role has been set up for this app, you see “Default Access” role selected. Normally there is no additional role to assign.
- In the Add Assignment dialog, click the Assign
Step 4: Configure Cisco ASA for SAML Authentication
You’ll now need to configure your ASA device. The CLI is the fastest method, but you can also use ASDM (we’ll cover that in another post soon).
Here’s the high level process:
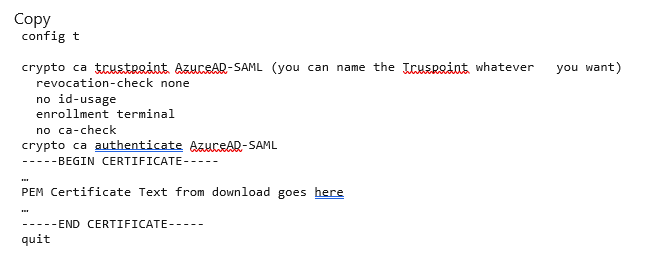
1. Create a Trustpoint and import the SAML cert.
2. Provision the SAML Identity Provider using the CLI
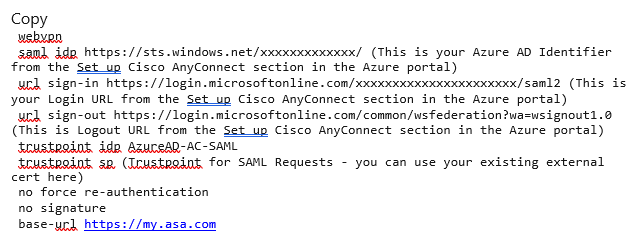
3. Apply SAML authentication to your VPN tunnel group.
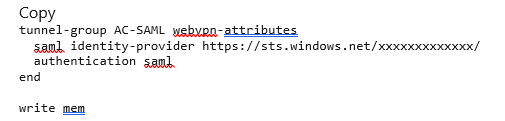
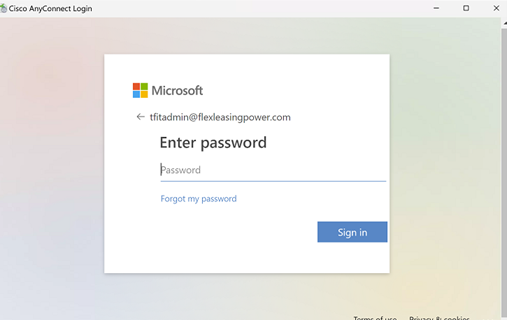
4. Then apply it to your tunnel group and you’re set. When you log in to that tunnel group, you’ll be re-directed to an Azure sign in.
Need to update your IdP config later? You’ll have to remove and reapply the SAML setup for the changes to take effect.
Pro Tips for Denver SMBs
-
If you’re in construction or energy, centralizing VPN access control like this is a big help when managing mobile teams or offsite contractors.
-
In professional services or healthcare, it can also support compliance goals (think HIPAA or FINRA) by improving auditability and credential security.
Getting your Azure AD VPN integration right takes a bit of upfront work, but the payoff in streamlined access and improved security is worth it.
If you’re not ready to do it alone, we’re one click away.

